What Is IoT Connectivity?
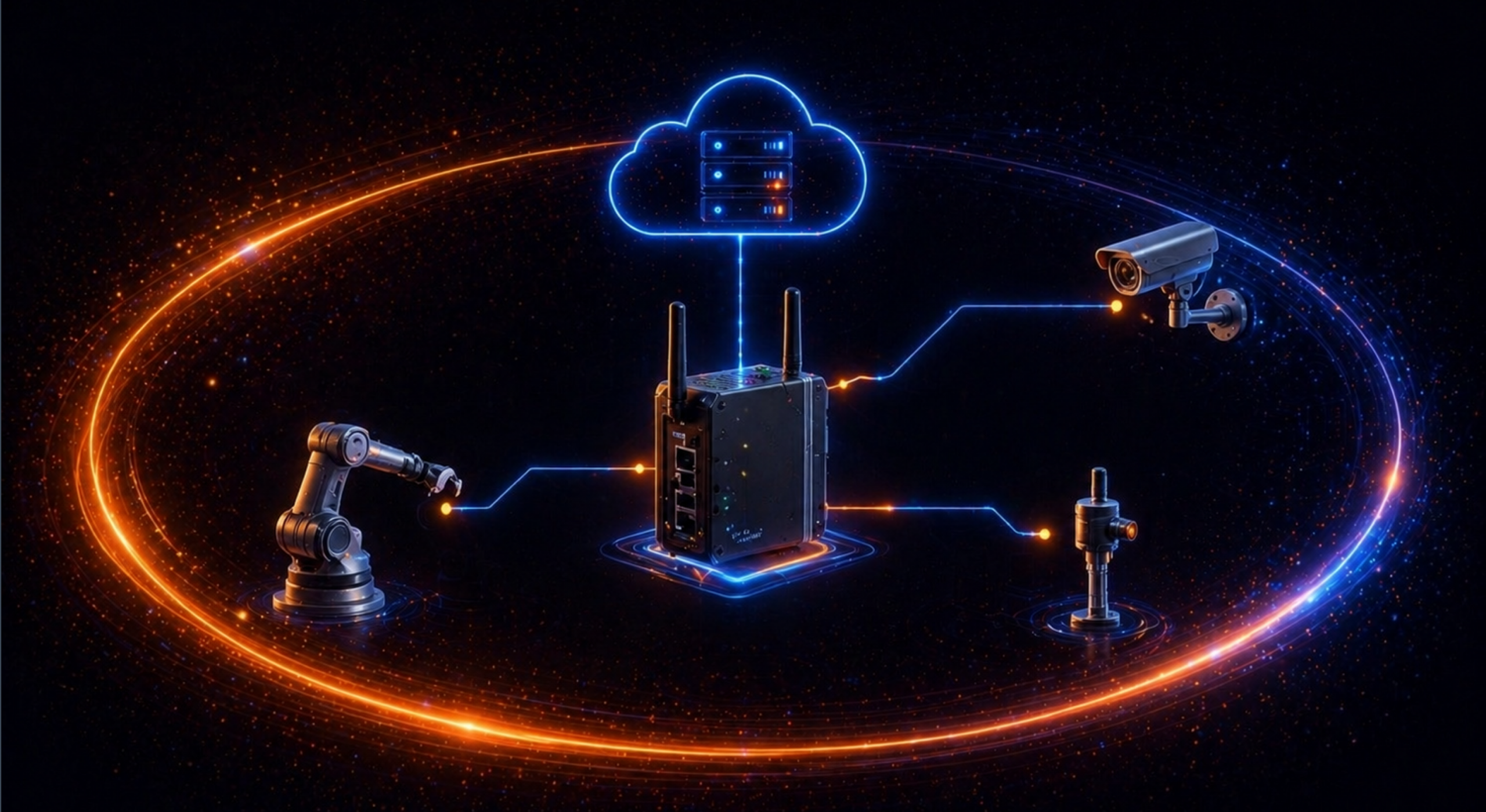
IoT connectivity refers to the technologies that enable devices to transmit data to the cloud / application server or other devices. It acts as the backbone for IoT, allowing sensors, machines, and smart devices to automate processes, facilitate real-time monitoring, and create actionable, data-driven insights.
Establishing reliable connectivity is essential for IoT because it transforms standalone devices into integrated systems capable of delivering valuable insights and automation. The type of connectivity chosen impacts device power consumption, data throughput, coverage area, and operational costs.
Key IoT connectivity technologies include:
- Cellular IoT: Highly reliable, suitable for mobile assets. Includes 4G/LTE, 5G for high-speed, and NB-IoT/LTE-M for low-power, wide-area needs.
- LPWAN (Low-Power Wide Area Network): Ideal for long-range, low-data, battery-operated sensors. Examples include LoRaWAN and Sigfox.
- Short-Range Wireless: Suitable for local, high-throughput, or power-constrained devices. Includes Wi-Fi, Bluetooth Low Energy (BLE), Zigbee, and NFC.
- Wired/Ethernet: Used for stationary, high-security, or high-bandwidth requirements.
This is part of a series of articles about IoT networking